By - Gaurav Vermma
Featured Events
May 04, 2026
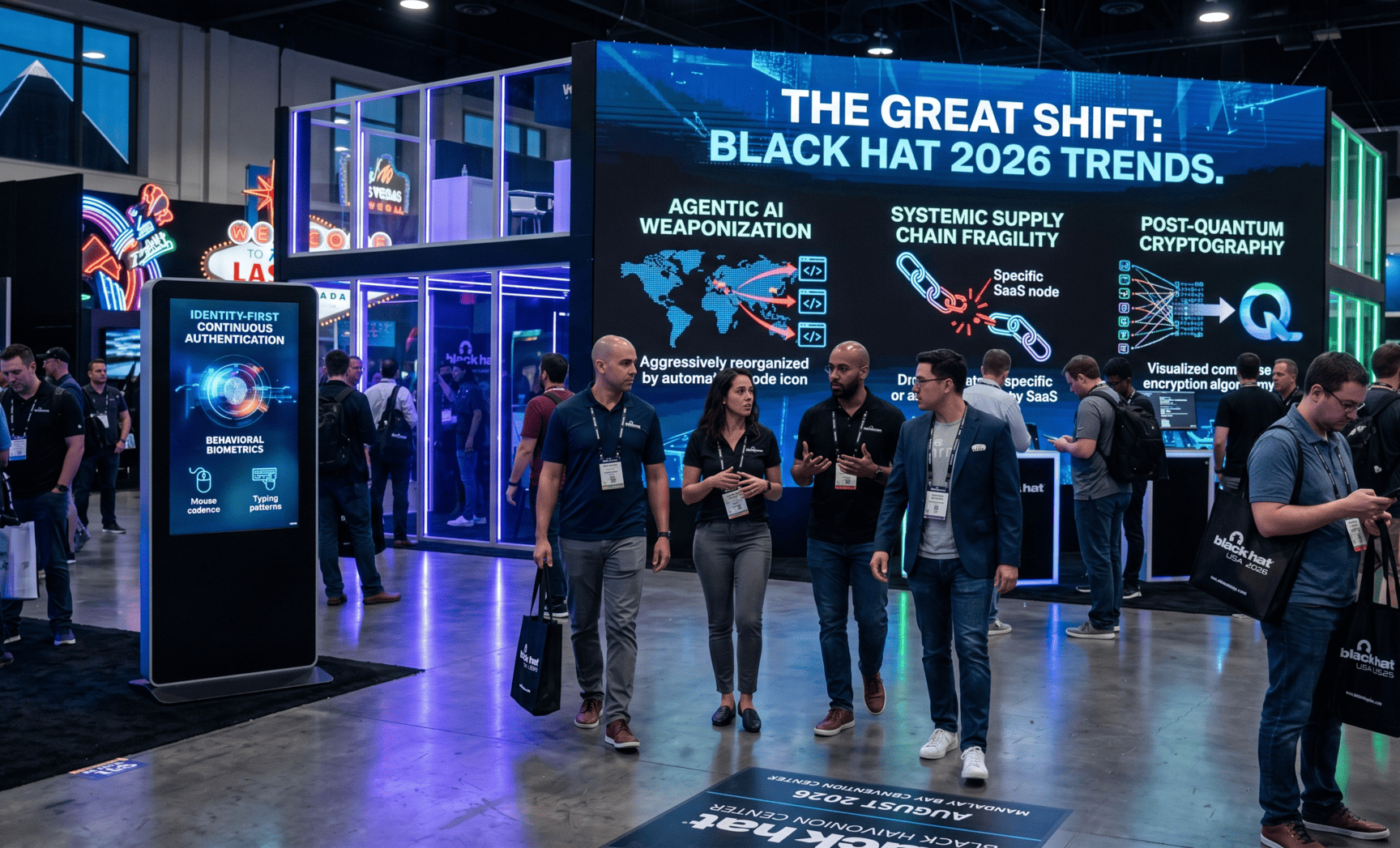
The Great Shift: Cybersecurity Trends to Watch at Black Hat 2026
If you’ve been following the pulse of InfoSec over the last decade, you know that the “perimeter” is a relic of the past. But as we gear up for Black Hat USA 2026 in Las Vegas, the conversation has moved beyond just “losing the perimeter.” We are now navigating an era where the attackers are autonomous, the data is decentralized, and the very math that protects our world is under threat.
This isn’t just another year of incremental updates. 2026 marks the point where Agentic AI and Quantum-Readiness move from the “future” category into the “urgent” category.
1. The Weaponization of Agentic AI
The biggest headline at Black Hat this year isn’t a single vulnerability; it’s the industrialization of the attack lifecycle. We are moving from “Generative AI” (which writes a phishing email) to Agentic AI (which conducts the entire reconnaissance, social engineering, and exfiltration process on its own).
The Autonomous Phishing Pipeline
In 2026, threat actors aren’t manually researching targets. They are deploying Autonomous AI Agents that can:
-
- Scrape professional networks for organizational charts.
- Monitor social media to mimic a CEO’s specific tone and vocabulary.
- Engage in real-time “human-like” text or voice conversations to bypass multi-factor authentication (MFA) via social engineering.
The Defensive Counter-Play: We will see a massive focus on AI-Driven Threat Hunting. Organizations are fighting fire with fire, using defensive agents that can spot these synthetic patterns faster than any human SOC analyst.
2. The Era of Systemic Supply Chain Risk
The “SolarWinds” era was a wake-up call, but 2026 is the year we face the full reality of Systemic Supply Chain Fragility. Attackers have realized that breaching a single, massive enterprise is hard, but breaching a niche SaaS provider used by 5,000 enterprises is efficient.
Beyond the SBOM
The Software Bill of Materials (SBOM) is no longer enough. The focus at Black Hat has shifted to VEX (Vulnerability Exploitability eXchange) and VSA (Verification of System Integrity).
-
- The Trend: Instead of just knowing what is in your software, security teams are demanding proof that the software hasn’t been tampered with at the build level.
- Targeting the CI/CD Pipeline: Expect several high-profile briefings on how “Agentic Malware” can now sit silently within developer environments, injecting malicious code only during the final production build to avoid detection.
3. Post-Quantum Cryptography (PQC): The “Harvest Now, Decrypt Later” Problem
While a functional, commercially viable quantum computer might still be on the horizon, the threat to cybersecurity is immediate. The buzzword at the 2026 briefings is “Harvest Now, Decrypt Later” (HNDL).
State-sponsored actors are currently stealing vast amounts of encrypted sensitive data with the plan to decrypt it once quantum technology matures.
-
- The Transition: Organizations are now racing to implement NIST-standardized Post-Quantum Cryptography.
- Crypto-Agility: Black Hat sessions will emphasize “Crypto-Agility”—the ability for a system to swap out encryption algorithms without tearing down the entire infrastructure.
4. Identity-First Security and the Death of the Password
In 2026, we have finally reached the tipping point for Passwordless Authentication. However, with the rise of AI-generated deepfakes, “Identity” has become more complex than ever.
The Rise of Identity Fabric
Security leaders are moving toward an Identity Fabric—a unified way to manage identities across cloud, on-premise, and edge environments.
-
- Continuous Authentication: We are moving away from “log in once and you’re in.” Systems in 2026 use Behavioral Biometrics (how you move your mouse, your typing cadence, your geo-velocity) to constantly verify that the person behind the screen is actually who they claim to be.
- Deepfake Defense: How do you verify a face on a Zoom call when AI can generate a perfect replica in real-time? Expect groundbreaking research on Liveness Detection and cryptographic watermarking for digital media.
5. Industrialized Ransomware and “Triple Extortion”
Ransomware hasn’t gone away; it has simply evolved into a professional service industry. Ransomware-as-a-Service (RaaS) now looks like a legitimate SaaS business, complete with help desks and tiered subscription models for hackers.
The Triple Extortion Tactic
We are seeing a move toward Triple Extortion:
-
- Encryption: Locking your data.
- Exfiltration: Threatening to leak the data.
- DDoS/Harassment: Launching a massive attack on your website or contacting your customers directly to tell them their data was stolen.
The sessions in Vegas this year will focus on Cyber Resilience—the idea that you will be hit, and your success depends on how fast you can recover without paying a cent.
Conclusion: Embracing the Proactive Frontier
The landscape of Black Hat 2026 makes one thing clear: the luxury of being reactive is gone. We are no longer defending against hackers; we are defending against automated systems that operate at machine speed. As we move from the “Perimeter” era into the “Agentic and Quantum” era, our survival depends on shifting our mindset from prevention to resilience.
To stay ahead, organizations must move beyond checking boxes on a compliance list. Success in 2026 requires an identity-centric approach, crypto-agility to withstand the coming quantum storm, and a supply chain strategy that demands integrity over mere visibility. The Vegas desert serves as a reminder that while the environment is harsh, those who adapt don’t just survive—they lead. The “Great Shift” is here; it’s time to decide if you’re the hunter or the hunted.